
KIDANVerse

KIDANVerse
End-to-end security operations monitoring.
Expert guidance for strategic technology decisions.
Enterprise services supporting critical IT infrastructure.
Seamless enterprise technology solution deployment.
Empower teams with expert-led technology programs.
Gain complete visibility into your technology infrastructur
Tailored IT solutions for operational excellence.
Expert on-demand consultation for technology procurement
Dedicated IT support for seamless operations.
Anything else ? please
contact us
Reach out to KIDAN for inquiries and support.
24/7 global technology operations center.
Expert guidance for strategic technology
decisions.
Learn more about KIDAN’s vision, values, and expertise.
Proactive security operations to
protect data asset
Intelligent operations control for
agile IT systems
Ensuring smooth network operations
and uptime 24/7
Anything else ? please
contact us
Expert guidance for strategic technology
decisions.
Learn more about KIDAN’s vision, values, and expertise.
Strategic Vendor Partners
Technical Managed Solutions
Enterprise clients across industry sectors
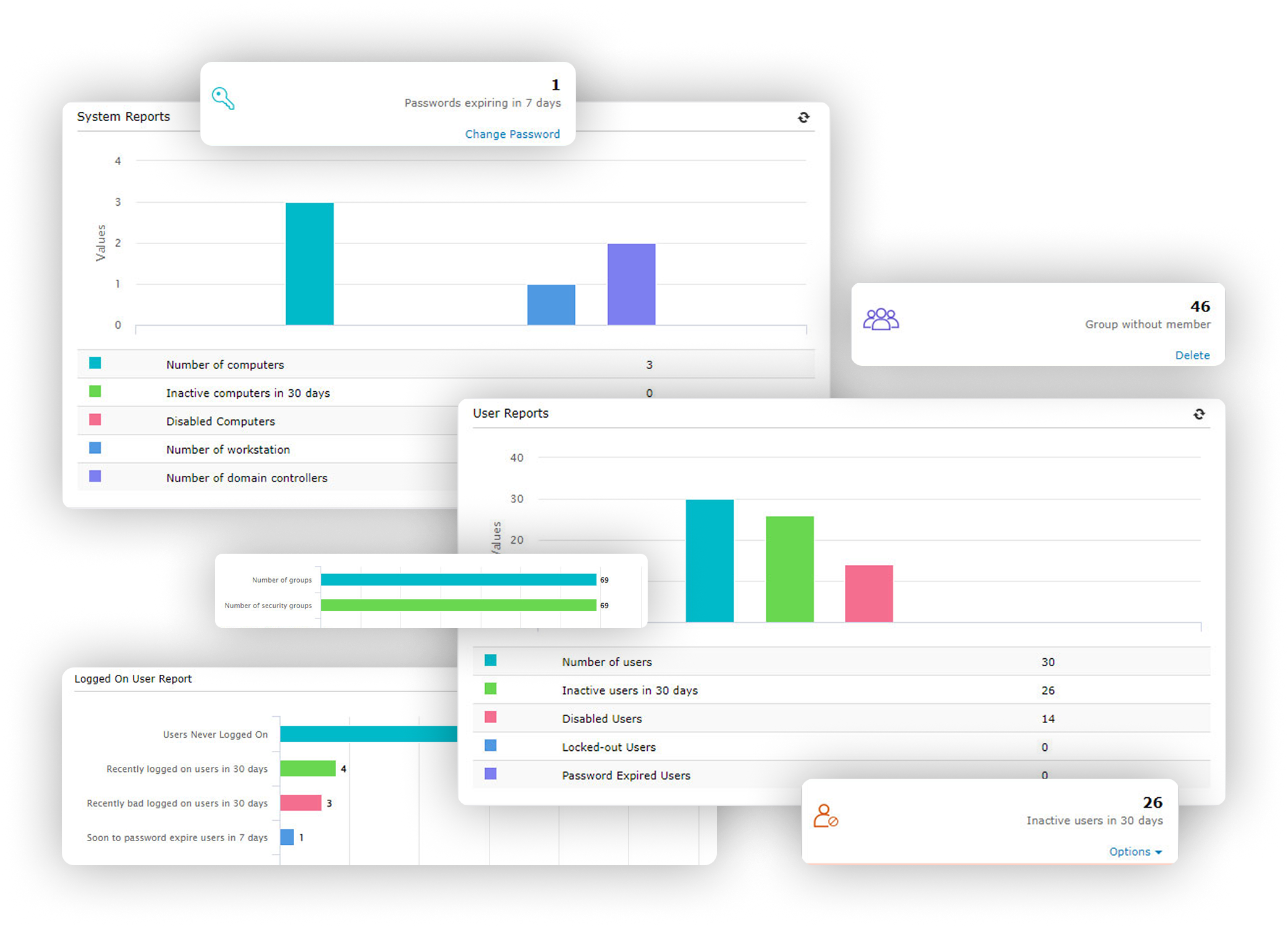
Reduce manual effort and free IT teams for strategic tasks.
Generate detailed reports on password expiration status, invalid logon attempts, and password changes.
Perform role-based security delegation and access control using security roles you create, thus minimizing errors.
Perform role-based security delegation and access control using security roles you create, thus minimizing errors.
Perform role-based security delegation and access control using security roles you create, thus minimizing errors.
Equip a user in an OU with administrative rights so they can perform specific tasks within the scope of the assigned OU, making it secure.
Configure and delegate admin rights to the help desk users and HR admins using a secure and non-invasive delegation model.
Automate Active Directory tasks using the review-approval workflow, template-controlled user provisioning, and user account management.
Back up all AD objects, like users, groups, GPOs, OUs, Exchange attributes, DNS information, computers, and contacts, and restore them either partially or completely.
Back up all the items in Gmail (including all emails, contacts, journals, notes, posts, and tasks), Calendar, and Google Drive data. Use these backups to restore any data when necessary, irrespective of when the data was deleted.
Reset passwords, unlock accounts, manage users, and approve requests on the go. Stay in control of your AD environment 24/7, no matter where you are.
Create or modify user accounts, disable or delete users, manage group memberships, and access real-time reports all from your mobile device.
Stay connected. Stay productive. Stay
protected.

Continuously monitor your AD and Microsoft 365 environments for potential identity risks. Get a unified risk score that reflects your security posture and helps prioritize remediation efforts.
Run scheduled access reviews to validate user and group permissions. Automatically revoke unnecessary privileges to enforce least privilege and prevent permission creep.

Visualize potential lateral movement paths attackers could exploit. Identify weak links in your identity infrastructure and proactively reduce your AD attack surface.

Simplify compliance with GDPR, HIPAA, SOX, and more. Built-in risk assessments and access reviews help meet audit requirements and strengthen incident response readiness.

Uncover hidden privilege chains and misconfigurations in AD. Break potential attack paths before they’re exploited, and secure access to critical systems.

Automate periodic reviews of user and group access across AD and Microsoft 365. Ensure only the right people have the right access at the right time.
Available on Azure Marketplace: It can also be hosted on Microsoft Azure, offering a SaaS-like experience.

Introducing KIDAN’s Endpoint Management and Security as a Service powered by our 24/7 Swiss-led Technology Operations Center (TOC)
Your Endpoint Central platform will be managed and optimized by certified engineers who live and breathe this technology. We handle all software deployments, policy configurations, and routine maintenance, ensuring the tool is always performing at its peak and aligned with the latest security best practices.
Move beyond raw data. We provide you with clear, executive-level monthly reports that translate technical activity into business-relevant insights. Understand your security posture, see the threats we’ve neutralized, and demonstrate compliance with ease.























Reset passwords, unlock accounts, manage users, and approve requests on the go. Stay in control of your AD environment 24/7, no matter where you are.
Create or modify user accounts, disable or delete users, manage group memberships, and access real-time reports all from your mobile device.

Stay connected. Stay productive. Stay
protected.

Continuously monitor your AD and Microsoft 365 environments for potential identity risks. Get a unified risk score that reflects your security posture and helps prioritize remediation efforts.

Run scheduled access reviews to validate user and group permissions. Automatically revoke unnecessary privileges to enforce least privilege and prevent permission creep.

Visualize potential lateral movement paths attackers could exploit. Identify weak links in your identity infrastructure and proactively reduce your AD attack surface.

Simplify compliance with GDPR, HIPAA, SOX, and more. Built-in risk assessments and access reviews help meet audit requirements and strengthen incident response readiness.

Uncover hidden privilege chains and misconfigurations in AD. Break potential attack paths before they’re exploited, and secure access to critical systems.

Automate periodic reviews of user and group access across AD and Microsoft 365. Ensure only the right people have the right access at the right time.



Get a free trial or reach out to our team to explore how we can help meet your specific requirements.
We don’t just provide software we partner with you to ensure it delivers real, lasting value. Whether you’re looking for light-touch guidance or full-scale operational support, we offer flexible service models tailored to your needs.
We’ll help you set up, onboard, and train your team.
We’ll help you set up, onboard, and train your team.Need help getting up and running? We’re with you every step of the way from setup and configuration to onboarding and training. Our experts ensure your team is confident, capable, and ready to go.
Prefer to stay hands-off? Let us run the tool for you. We’ll handle everything monitoring, maintenance, updates, and optimization so you can focus on what matters most: your
business.
As your technology partner, we are committed to growing with you and tailoring the best model for your needs.

Director - IT
DRS Defense Solutions
While a CSP provides essential licensing, a system integrator (SI) partner like KIDAN provides the strategic wrapper addition and special pricing that unlocks the value of that license. We focus on the architecture, 24/7 security operations, and continuous management that transforms your Microsoft investment from a recurring cost into a secure, efficient, and resilient business platform. We ensure you use what you pay for, securely and effectively.
While a CSP provides essential licensing, a system integrator (SI) partner like KIDAN provides the strategic wrapper addition and special pricing that unlocks the value of that license. We focus on the architecture, 24/7 security operations, and continuous management that transforms your Microsoft investment from a recurring cost into a secure, efficient, and resilient business platform. We ensure you use what you pay for, securely and effectively.
The Free edition of ADManager Plus can be used to manage up to 100 objects in a single domain and cannot have more than one domain configured.
The Professional edition can be used to manage the number of domains and objects for which it is licensed for.
The Free edition can be upgraded to Professional edition at any point of time by obtaining a valid license from ZOHO Corp.
While a CSP provides essential licensing, a system integrator (SI) partner like KIDAN provides the strategic wrapper addition and special pricing that unlocks the value of that license. We focus on the architecture, 24/7 security operations, and continuous management that transforms your Microsoft investment from a recurring cost into a secure, efficient, and resilient business platform. We ensure you use what you pay for, securely and effectively.

Your application is now under review. Our team will carefully evaluate your use case, commitment level, and strategic fit. If shortlisted, you will hear from us within 5 business days to schedule your Discovery Call.
Almost there – a few quick details first.