Reach out to KIDAN for inquiries and support.
Expert guidance for strategic technology decisions.
24/7 global technology operations center.
Seamless enterprise technology solution deployment.
Empower teams with expert-led technology programs.
Enterprise services supporting critical IT infrastructure.
Tailored IT solutions for operational excellence.
End-to-end security operations monitoring.
Dedicated IT support for seamless operations.
Anything else ? please
contact us
Reach out to KIDAN for inquiries and support.
24/7 global technology operations center.
Expert guidance for strategic technology decisions.
Learn more about KIDAN’s vision, values, and expertise.


Gartner peerinsights customers’ choice 2021 for SIEM

7th time in Gartner Magic Quadrant, 2024
2nd in Best Event Log Analysis tools, 2020

1st in Top 10 SIEM Solutions
2nd Time Champion, 2020

Expert’s Choice Great UX
Without endpoint management, chaos, risk, and inefficiency
are inevitable.
Without endpoint management, chaos, risk, and inefficiency
are inevitable.


Safeguard elevated system activities performed on standard user accounts with MFA for Windows UAC.
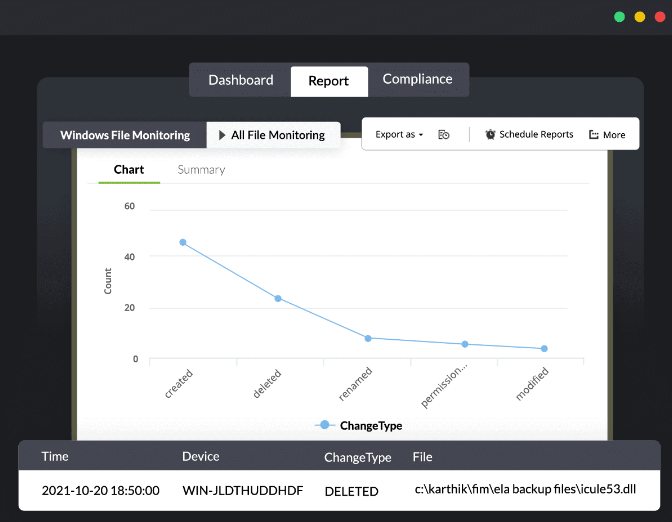
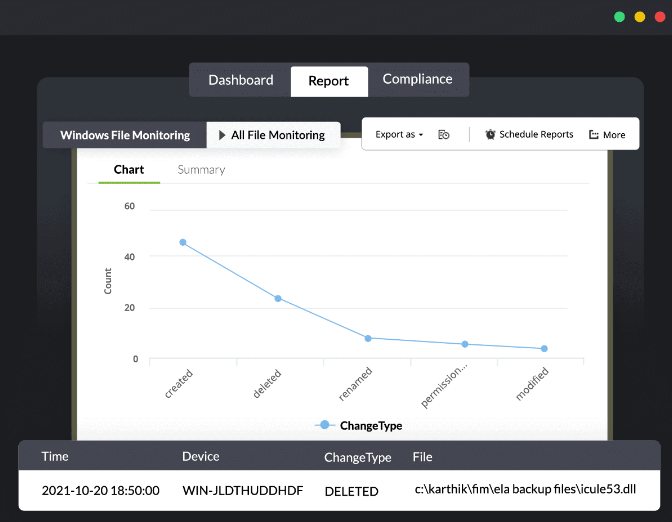
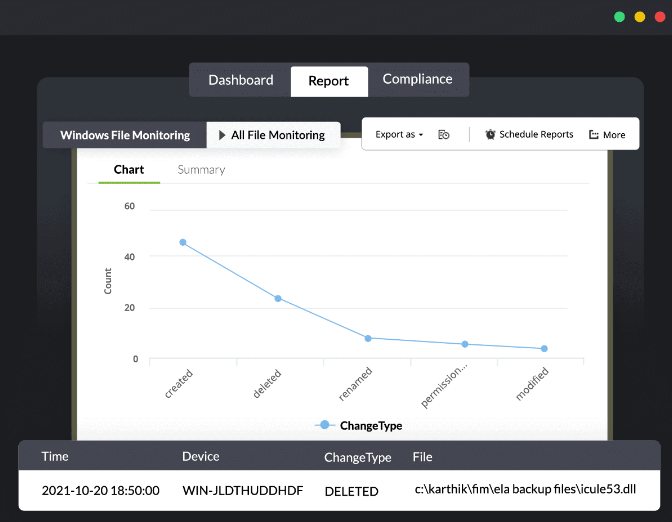
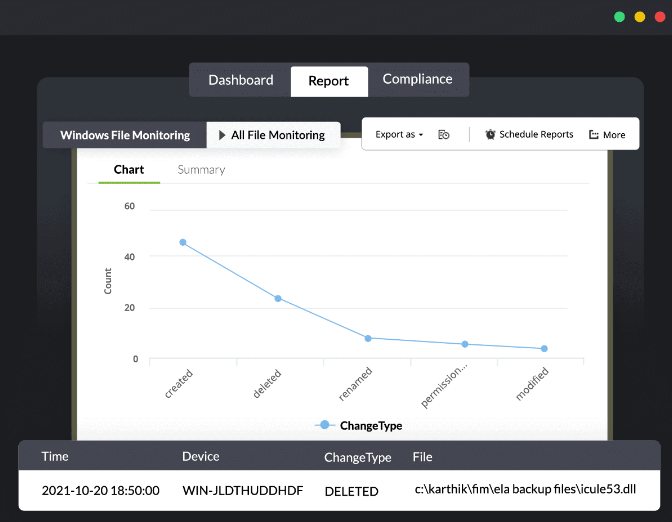
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.

Introducing KIDAN’s Endpoint Management and Security as a Service powered by our 24/7 Swiss-led Technology Operations Center (TOC)
Our TOC operates around the clock to monitor your endpoints. We don’t just send you alerts; we actively investigate, validate, and remediate threats before they can impact your operations. This includes vulnerability management, patch deployment, and enforcing security configurations across your entire fleet of devices.
Your Endpoint Central platform will be managed and optimized by certified engineers who live and breathe this technology. We handle all software deployments, policy configurations, and routine maintenance, ensuring the tool is always performing at its peak and aligned with the latest security best practices.
Move beyond raw data. We provide you with clear, executive-level monthly reports that translate technical activity into business-relevant insights. Understand your security posture, see the threats we’ve neutralized, and demonstrate compliance with ease.






























We don’t just provide software we partner with you to ensure it delivers real, lasting value. Whether you’re looking for light-touch guidance or full-scale operational support, we offer flexible service models tailored to your needs.
Start with the right license and unlock full
value.
Already have the tool or just getting started? We’ll help you provision the right licenses and guide you to unlock the full potential of your investment. Think of us as your strategic advisor always available, never intrusive.
We’ll help you set up, onboard, and train your team.
We’ll help you set up, onboard, and train your team.Need help getting up and running? We’re with you every step of the way from setup and configuration to onboarding and training. Our experts ensure your team is confident, capable, and ready to go.
We’ll help you set up, onboard, and train your team.
Prefer to stay hands-off? Let us run the tool for you. We’ll handle everything monitoring, maintenance, updates, and optimization so you can focus on what matters most: your
business.
Working with computers always involve authentication which is usually done by the user name and password combination. Now, when use ADSelfService Plus to reset Windows password or to unlock your locked-down account, first, the solution has to authenticate identity.
To do this, the solution uses any or all of the following methods depending on your IT administrator’s preference. Providing the information for the authentication, is called the enrollment process
ADSelfService Plus services can be categorized as Enrollment Requiring Services & Non-Enrollment Services.
Registration is needed to use the primary functions of ADSelfService Plus.
When ADSelfService Plus is used to reset the Windows password or to unlock a locked-down account. First, the solution has to authenticate the identity. To do this, the solution uses any or all of the following methods depending on the IT administrator’s preference. Providing the information for the authentication is called the enrollment process.
Logon to ADSelfService Plus and edit the enrollment data. For example, the security question is “What is your favorite movie?” to which the answer is “Cast Away”. However, now the need to update the answer to “Transformer”, logon, and edit the “Security Answer” any time.
Being the Swiss Partner of ManageEngine, Kidan is responsible for aiding with professional services, such as installing, implementing, configuring, training, and supporting the company to ensure an effective on-boarding of ADSelfService Plus.



Safeguard elevated system activities performed on standard user accounts with MFA for Windows UAC.
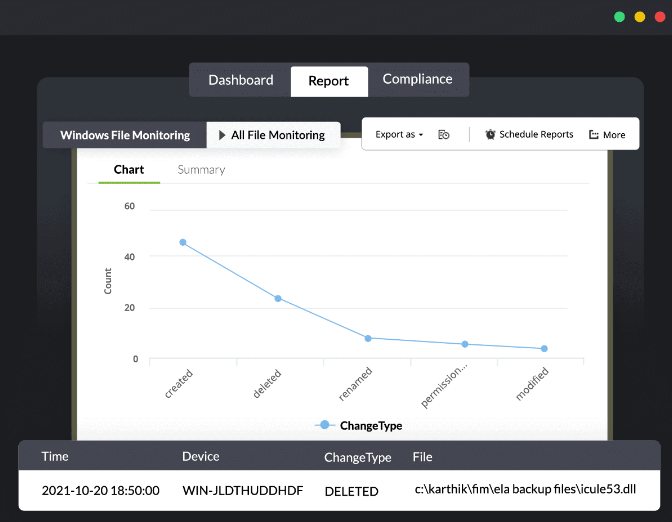
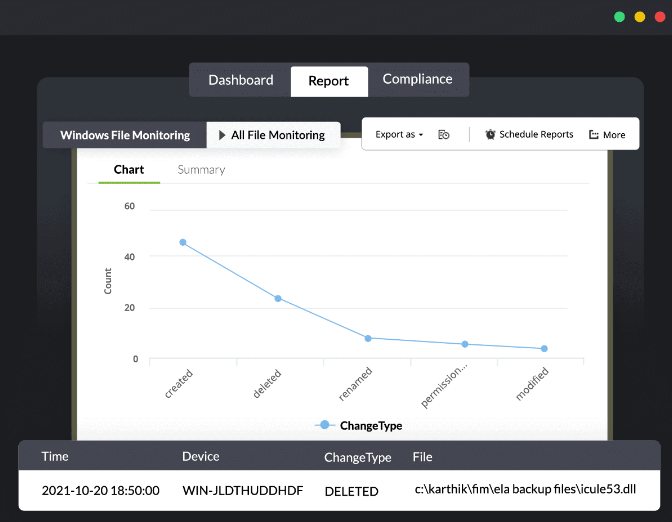
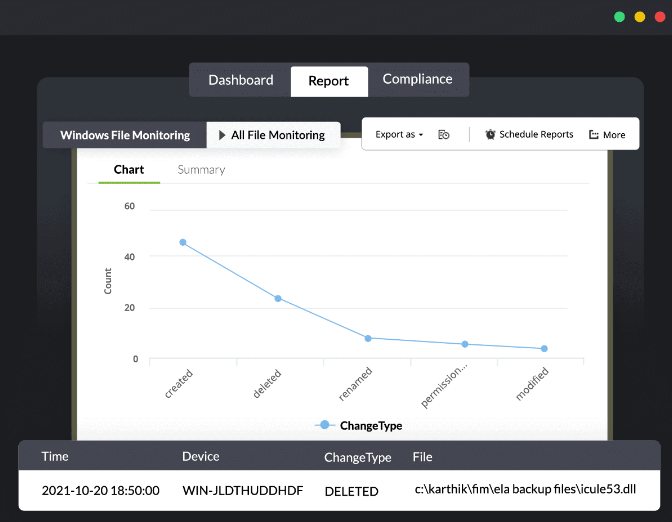
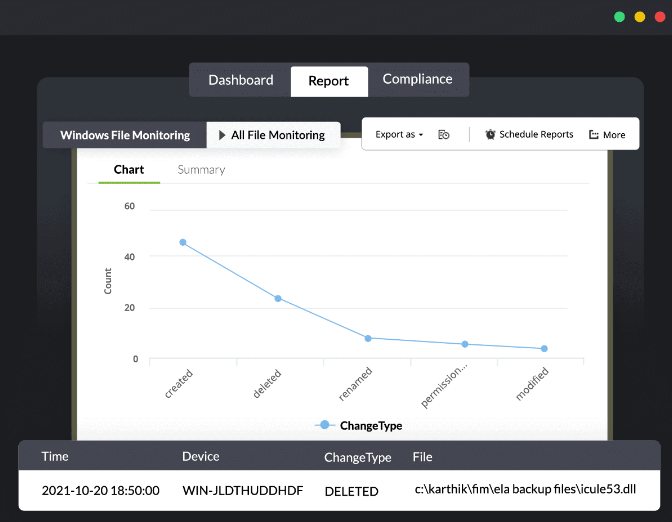
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
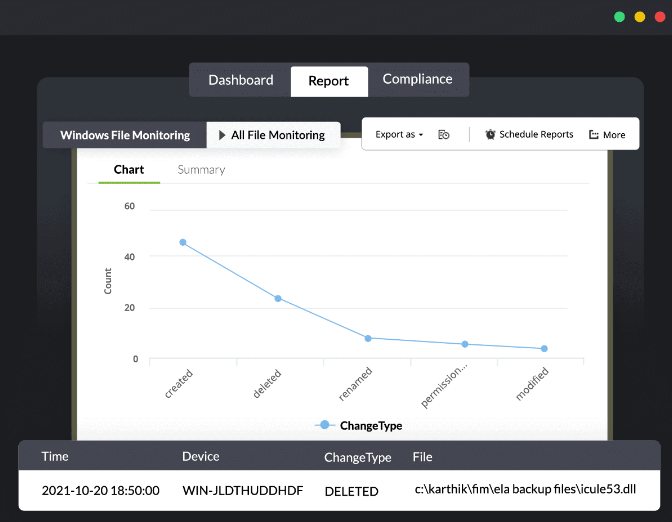
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
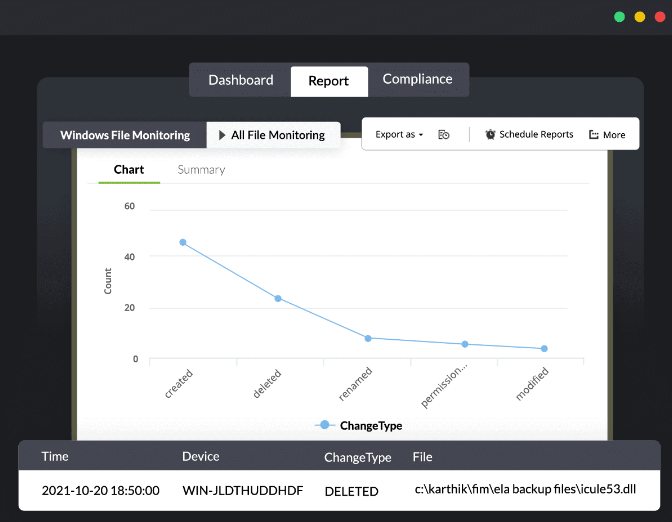
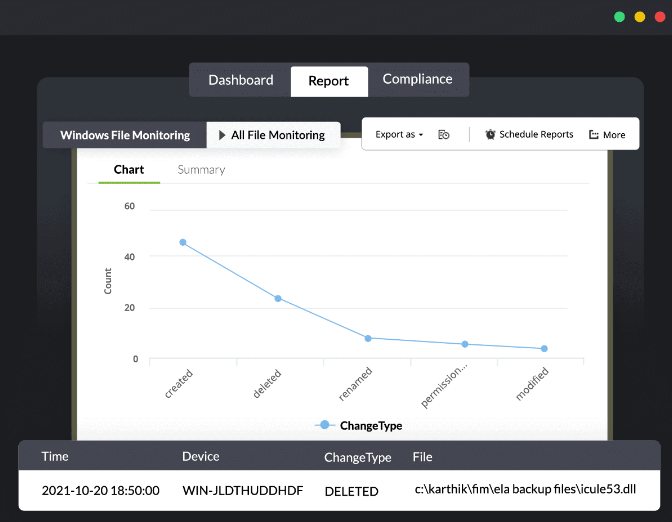
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
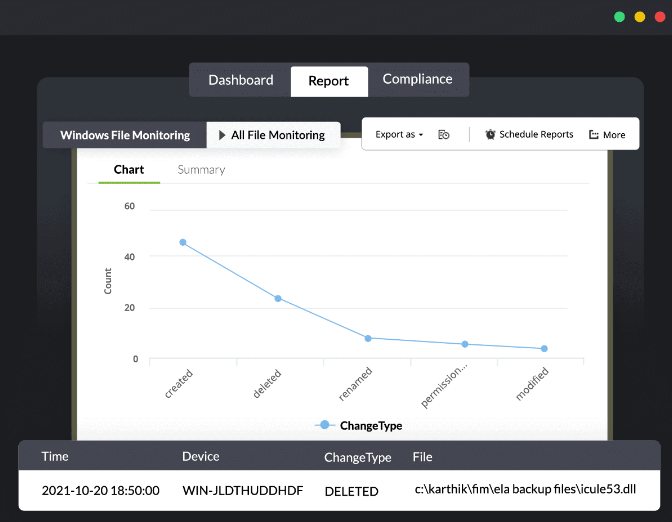
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
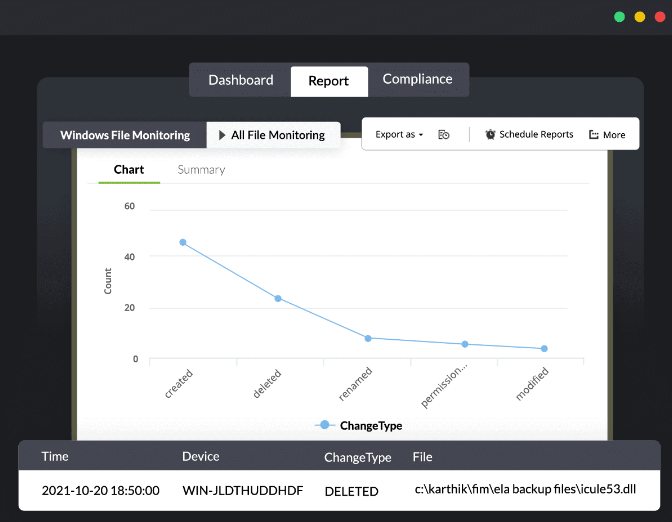
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.
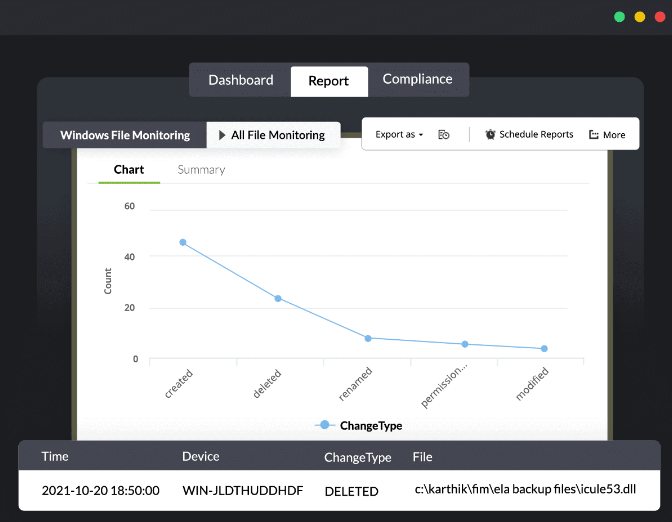
Collect and analyze logs from all your end-user devices on a single console.
Collect and analyze syslogs from various devices and gain insights on network activities that are displayed through intuitive graphs and reports.
Collect logs from multiple log sources such as Windows and Unix and Linux systems, IBM AS/400, applications, databases, firewalls, routers, switches, IDS/IPS, and your Cloud infrastructure.
Manage application logs and gain in-depth security information on incidents through predefined reports and real-time alerts.
Collect, filter, parse, analyze, correlate, search, and archive event logs.































We don’t just provide software we partner with you to ensure it delivers real, lasting value. Whether you’re looking for light-touch guidance or full-scale operational support, we offer flexible service models tailored to your needs.
Start with the right license and unlock full
value.
Already have the tool or just getting started? We’ll help you provision the right licenses and guide you to unlock the full potential of your investment. Think of us as your strategic advisor always available, never intrusive.
We’ll help you set up, onboard, and train your team.
We’ll help you set up, onboard, and train your team.Need help getting up and running? We’re with you every step of the way from setup and configuration to onboarding and training. Our experts ensure your team is confident, capable, and ready to go.
We’ll help you set up, onboard, and train your team.
Prefer to stay hands-off? Let us run the tool for you. We’ll handle everything monitoring, maintenance, updates, and optimization so you can focus on what matters most: your
business.
Working with computers always involve authentication which is usually done by the user name and password combination. Now, when use ADSelfService Plus to reset Windows password or to unlock your locked-down account, first, the solution has to authenticate identity.
To do this, the solution uses any or all of the following methods depending on your IT administrator’s preference. Providing the information for the authentication, is called the enrollment process
ADSelfService Plus services can be categorized as Enrollment Requiring Services & Non-Enrollment Services.
Registration is needed to use the primary functions of ADSelfService Plus.
When ADSelfService Plus is used to reset the Windows password or to unlock a locked-down account. First, the solution has to authenticate the identity. To do this, the solution uses any or all of the following methods depending on the IT administrator’s preference. Providing the information for the authentication is called the enrollment process.
Logon to ADSelfService Plus and edit the enrollment data. For example, the security question is “What is your favorite movie?” to which the answer is “Cast Away”. However, now the need to update the answer to “Transformer”, logon, and edit the “Security Answer” any time.
Being the Swiss Partner of ManageEngine, Kidan is responsible for aiding with professional services, such as installing, implementing, configuring, training, and supporting the company to ensure an effective on-boarding of ADSelfService Plus.



We don’t just provide software we partner with you to ensure it delivers real, lasting value. Whether you’re looking for light-touch guidance or full-scale operational support, we offer flexible service models tailored to your needs.
Start with the right license and unlock full
value.
Already have the tool or just getting started? We’ll help you provision the right licenses and guide you to unlock the full potential of your investment. Think of us as your strategic advisor always available, never intrusive.
We’ll help you set up, onboard, and train your team.
We’ll help you set up, onboard, and train your team.Need help getting up and running? We’re with you every step of the way from setup and configuration to onboarding and training. Our experts ensure your team is confident, capable, and ready to go.
We’ll help you set up, onboard, and train your team.
Prefer to stay hands-off? Let us run the tool for you. We’ll handle everything monitoring, maintenance, updates, and optimization so you can focus on what matters most: your
business.
Working with computers always involve authentication which is usually done by the user name and password combination. Now, when use ADSelfService Plus to reset Windows password or to unlock your locked-down account, first, the solution has to authenticate identity.
To do this, the solution uses any or all of the following methods depending on your IT administrator’s preference. Providing the information for the authentication, is called the enrollment process
ADSelfService Plus services can be categorized as Enrollment Requiring Services & Non-Enrollment Services.
Registration is needed to use the primary functions of ADSelfService Plus.
When ADSelfService Plus is used to reset the Windows password or to unlock a locked-down account. First, the solution has to authenticate the identity. To do this, the solution uses any or all of the following methods depending on the IT administrator’s preference. Providing the information for the authentication is called the enrollment process.
Logon to ADSelfService Plus and edit the enrollment data. For example, the security question is “What is your favorite movie?” to which the answer is “Cast Away”. However, now the need to update the answer to “Transformer”, logon, and edit the “Security Answer” any time.
Being the Swiss Partner of ManageEngine, Kidan is responsible for aiding with professional services, such as installing, implementing, configuring, training, and supporting the company to ensure an effective on-boarding of ADSelfService Plus.
Almost there – a few quick details first.